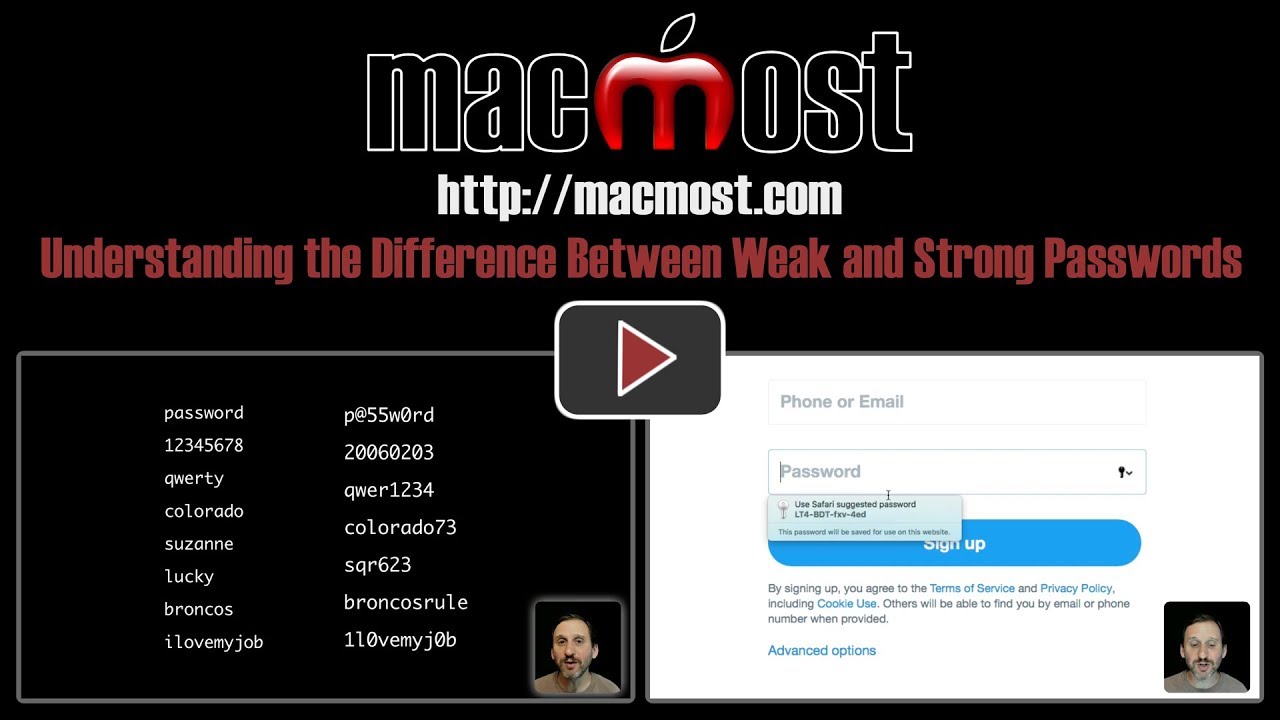
Most people understand that passwords with names or words in them are weak and shouldn't be used. But what people consider strong passwords are often weak passwords as well. Substituting numbers or special characters for letters, using dates, and combining words does not make a password strong. The only way to get truly strong passwords is to let the computer randomly generate them for you.
▶ You can also watch this video at YouTube.
▶
▶

I understand the need for strong passwords. But companies could greatly help prevent hacking by implementing a "3 strikes and you're out" password system, i.e., three wrong password tries and your account is suspended for 24 hours. No hacker or Bot would try just three passwords day after day after day ...
Tony: That only prevents someone from breaking into a single, targeted account. But most of the time each attempt is a random ID (email) and random password. So if there are 100 million Apple IDs (iCloud email addresses) then the bot tries one Apple ID, one password. Then it moves to another Apple ID, another password. It keeps doing this until it gets 1,000 valid combinations and then sells those or whatever. So three strikes wouldn't work as no one account would get more than a single strike in such an attack.
A lot of sites have certain rules about passwords only being alpha numeric. Can I get KeyChain to supply random passwords in this format?
Brenda: Hopefully, you don't come across many of these sites anymore. Those kinds of restrictions only work to make passwords weaker. If you do find one you can always allow Safari to suggest a password, and then remove those characters yourself.
Hi Gary, Where can I go to learn basic user understanding of Keychain? For example, how to retrieve a password from it. Iknow I can go to Apple but I like your step by step videos.
Noni: https://macmost.com/safari-passwords.html
Hi Gary, most banks and credit card sites will not allow autofill or ask for specific letters or numbers form your password . How should we cope with this, please?
Gordon: I hope that this kinda of thing is getting rarer as limiting what you can use in a password greatly weakens the password. But if you still find a site that insists on some nonsense like this, then you can try just using the autofill password and deleting the extra characters. That way it is still random, at least.
You forgot to mention the utilization of 2 step verification if sites offer it
Interesting video. I like using Keychain Access - but how to make a secure Keychain Access password? That password I will have to remember...
G Ludington: Yes, there are lots of other aspects, but I wanted to deal strictly with this one topic here. I've got a free online course on Mac Security (see right sidebar here) and is a few hours long and covers those things.
Janus: In Keychain access you have the ability to generate passwords. You can use that to create a good random one to use for your user login.
Thanks Gary.
One trick I use is to create (and remember) "nonsense" words within a password is the use the first letter of each word in a song title (or common saying):
On The Road Again - otra
Willie Nelson's On The Road Again = wnotra
Early To Bed, Early To Rise = etbetr
Then I might easy to remember years (birth year digits in order, or out of order.)
And, "favorite" special characters. I like "@".
-=Gr@nt M@cL@ren=-
Gary Rosenzweig@nt: Actually, this is exactly what I am warning against in the video. Those are all examples of weak passwords. You shouldn't use any of those, or combinations. You need to use randomly-generated passwords.
Gary, if I would replace all my passwords by Safari-generated ones and then depend upon iCloud Keychain, are the passwords encrypted and stored locally across all my devices (and then new/changed ones sync'd via iCloud), or do the devices need iCloud access in order to fill them in? I realize if wifi or internet is down I wouldn't be online anyway, but there is a chance I might be online but unable to connect with iCloud. I fear giving up complete control here.
Ron: iCloud encrypts the passwords. iCloud stores them locally for time you don't have access, but obviously updates to those passwords won't work until you are connected.
What if myMac book pro...Safari crashes?? how do I retrieve the keychain passwords??
Kay: If Safari crashes, then just restart it. If you can't run Safari at all, then you've got problems that you need to fix. You can always use the Keychain Access app on your Mac to get to your password another way temporarily while you fix it.
Is it possible to print a physical copy of your Keychain passes to keep locked away?
Jasper: Not really possible. I guess this is too much of a risk -- someone gets access to your computer for a few seconds, prints all (to a PDF or whatever), and takes them. YOu can always look through them, grab your most important passwords to critical sites, and copy and paste those into a document to print (and delete the document).
Hi Gary,what if I use generated password from Keychain and then my Mac crashes and is formated and the back up got corrupt,so I start with completely new machine.Where shall I look for those passwords?Are they lost?
Lubomir: If you are using iCloud Keychain, then no, they are not lost. Just log on to iCloud with your new Mac. Also, most systems have password recovery options. What happens if you forget your passwords now?